Introduction
SSO integration configuration using OpenID Connect (OIDC) involves both your identity provider and the OpsRamp platform to configure redirects to your custom branding URL.
OIDC is a modern authentication protocol built on top of OAuth 2.0 that enables secure user identity verification through token-based authentication.
Prerequisites
- Partners register with OpsRamp to get login credentials.
- Provide a custom branding URL, such as <yourwebsitename>.opsramp.com.
- Access to your identity provider with permissions to create and manage OIDC applications.
- The following values from your identity provider:
- Issuer URL
- Authorization Endpoint
- Token Endpoint
- JWKS URI
- Logout URL
- Client ID and Client Secret
Configure Your Identity Provider OIDC Application
Before configuring OpsRamp, set up an OIDC application in your identity provider:
Log in to your identity provider’s admin console.
Navigate to the application management section and create a new OIDC or OAuth 2.0 application.
Select Web Application as the application type.
Configure the following settings:
- App name: Enter a name, for example,
OpsRamp OIDC. - Grant type: Select Authorization Code.
- Sign-in redirect URI: Enter the OpsRamp callback URL.
Example:https://<yoursubdomain>.app.opsramp.com/sso/oidc/callback - Sign-out redirect URI: Enter the OpsRamp logout URL.
Example:https://<yoursubdomain>.app.opsramp.com
- App name: Enter a name, for example,
Save the application and note the following values:
- Client ID
- Client Secret
From your identity provider’s discovery document or well-known configuration endpoint, retrieve the following URLs:
- Issuer URL
- Authorization Endpoint (
authorization_endpoint) - Token Endpoint (
token_endpoint) - JWKS URI (
jwks_uri) - Logout URL (
end_session_endpoint)
The discovery document is typically available at:
https://<your-idp-domain>/.well-known/openid-configuration
OpsRamp Configuration
Click All Clients, select a client.
Click Setup > Account.
Select the Integrations tile.
The Installed Integrations screen is displayed, with all the installed applications. Click + ADD on the Installed Integrations page.
If you do not have any installed applications, you will be navigated to the Available Integrations page. The Available Integrations page displays all the available applications along with the newly created application with the version.
Search for Custom (SSO) using the search option available. Alternatively, use the All Categories option to search.
Click +Add on the Custom (SSO) tile.
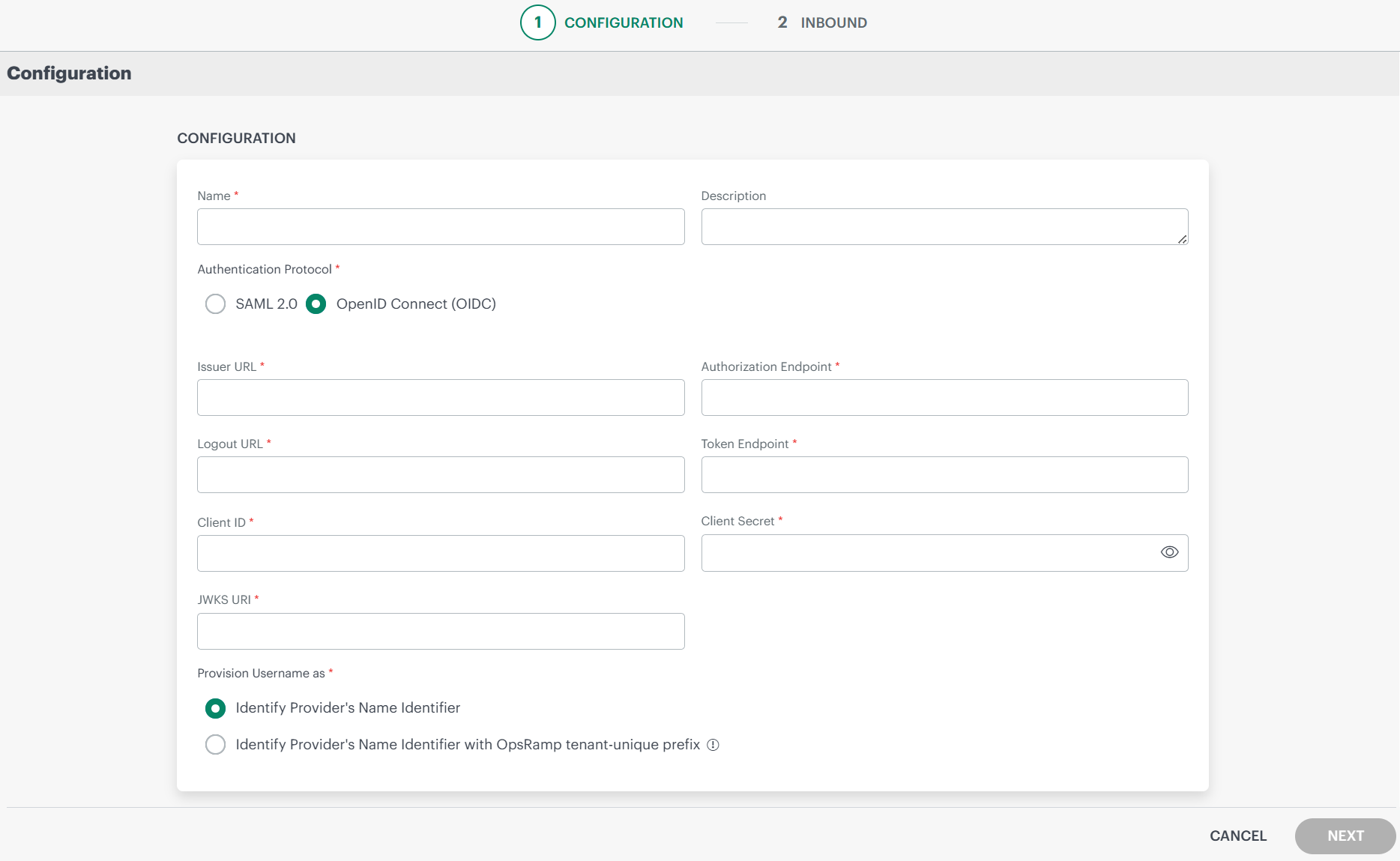
Authentication Protocol: Select OpenID Connect (OIDC).Enter the following information in the Configuration page:
- Name (Required): Enter a unique name for the integration.
- Description: Provide a description for the integration.
- Issuer URL (Required): The base URL that identifies your authorization server. It is used to validate tokens and discover OIDC configuration metadata.
Example:https://idp.example.com/oauth2/default - Authorization Endpoint (Required): The endpoint used to initiate the authentication request. It redirects users to your identity provider for authentication and consent.
Example:https://idp.example.com/oauth2/default/v1/authorize - Logout URL (Required): The endpoint used to log out of the identity provider session and optionally redirect after logout.
Example:https://idp.example.com/oauth2/default/v1/logout - Token Endpoint (Required): The endpoint used to exchange an authorization code for access and ID tokens.
Example:https://idp.example.com/oauth2/default/v1/token - Client ID (Required): A unique identifier assigned to the OpsRamp application during registration in your identity provider. It is used to identify the client during authentication requests.
Example:a1b2c3d4e5f6g7h8i9j0 - Client Secret (Required): A confidential key generated by your identity provider for the application. It is used to authenticate the client when requesting tokens from the token endpoint.
Example:A1b2C3d4E5f6G7h8I9j0K1l2M3n4O5p6Q7r8S9t0 - JWKS URI (Required): The JSON Web Key Set (JWKS) endpoint that provides the public keys used to verify the signature of ID tokens and access tokens issued by your identity provider.
Example:https://idp.example.com/oauth2/default/v1/keys
Provision Username as: There are two ways to provision a user. Select the appropriate option:
Identify Provider’s Name Identifier option is selected by default. The user which is created in the SSO portal will reflect in OpsRamp.
Identify Provider’s Name Identifier with OpsRamp tenant-unique prefix: This option allows you to:
- Create usernames with a unique 3-digit alphanumeric prefix, that is generated automatically by the system.
- Install the same identity provider across multiple OpsRamp tenants.
Note: Once you enable this option and install the integration, you cannot revert your changes.
Example: There are three partners, Partner P1, P2, and P3. Each partner has usernames created with unique 3-digit alphanumeric prefix, like g0z.username1 for partner P1, p0w.username1 for partner P2, and t9q.username1 for partner P3.
Click Next.
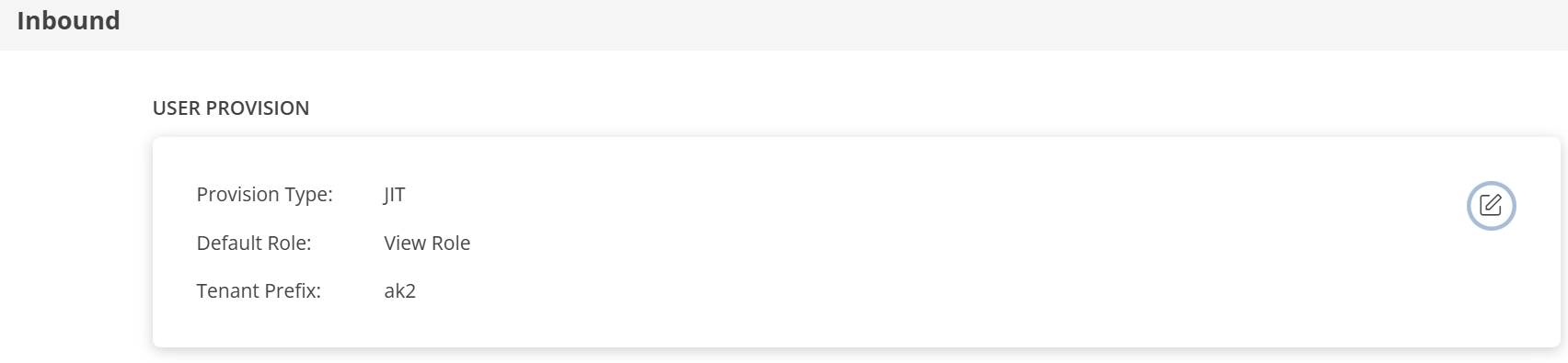
In the Inbound page, there are two sections: USER PROVISION and MAP ATTRIBUTES.
USER PROVISION
OpsRamp supports the following user provisioning methods:
- JIT
- NONE: Only the existing users will be able to login.
JIT
Following section describes JIT provisioning in detail.
In the Inbound page:
- Click the edit icon, enter the following details, and click UPDATE USER PROVISION:
- Provision Type: Select JIT. When configuring the integration it is necessary to select the Provision Type - JIT to synchronize users when provisioning occurs.
- Default Role: The required user role.
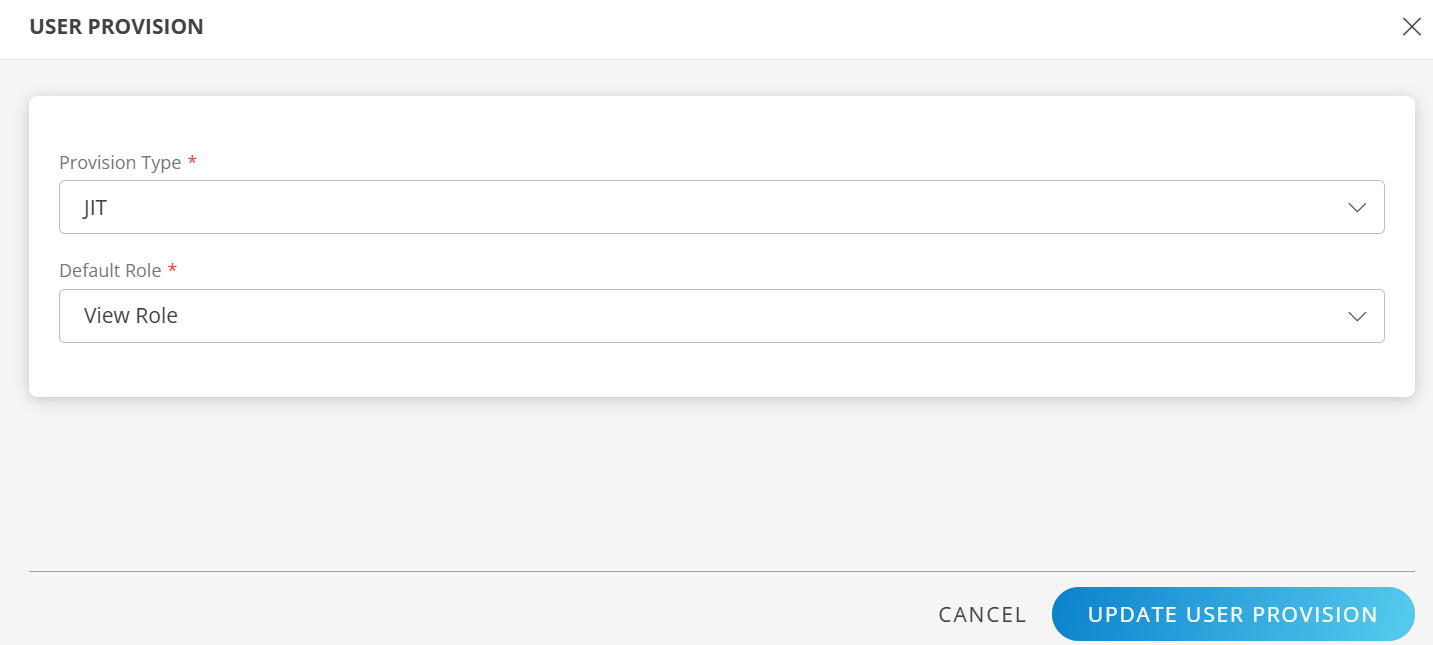
The details are updated and the USER PROVISION section displays the unique Tenant Prefix. These details are used when configuring custom SSO Provisioning settings.
MAP ATTRIBUTES
Define the following Map Attributes:
Note:
- For JIT: The OpsRamp properties like Primary Email, First Name, Last Name, and Role are required.
- Click +Add in the Map Attributes section.
- From the Add Map Attributes window, enter the following information:
User:
- Select OpsRamp Entity as User and OpsRamp Property as Role.
Role mapping is required for User and User Group.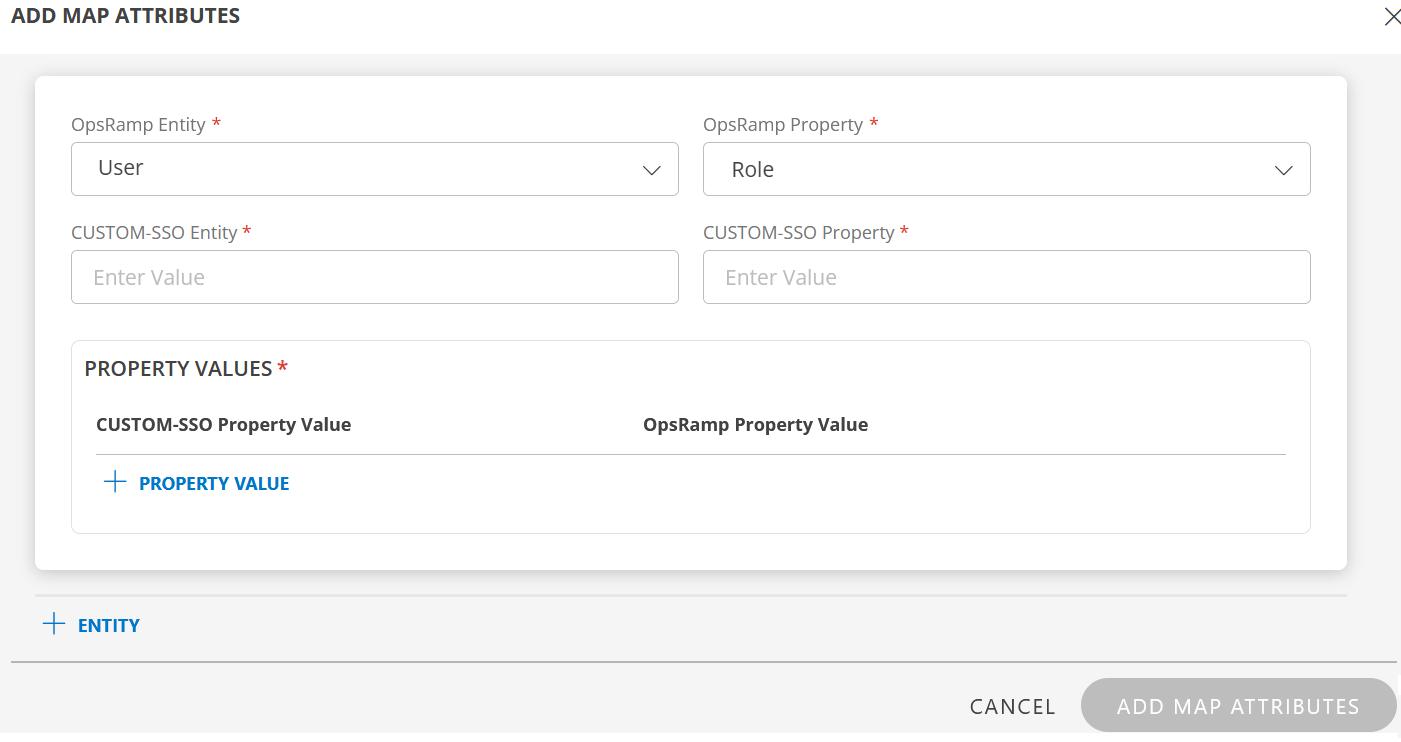
- Custom-SSO Entity: Enter the value.
- Custom-SSO Property: Enter the value.
In PROPERTY VALUES section: - Custom-SSO Property Value: The user details in the OIDC ID token claims received by OpsRamp contains the field information. Ensure that you provide the value of the field in this box.
- Example ID token claims:
{ "sub": "user-unique-id-001", "name": "User Name1", "given_name": "User", "family_name": "Name1", "email": "user.name1@example.com", "email_verified": true, "groups": [ "Everyone", "OpsRamp-Admins" ], "zoneinfo": "America/Los_Angeles", "phone_number": "+1-1234567890" } - OpsRamp Property Value: Select the appropriate role corresponding to the Custom-SSO Property Value.
- Click Save. The mapping is saved and displayed.
To add more property values click +Property Value.
Use the Filter option to filter the map attributes.
Similarly, map attributes for other entities.
Note: If mapping for Time Zone is not provided, then organization timezone is considered by default.
User Group:
- Select OpsRamp Entity as User Group and OpsRamp Property as Role.
- Custom-SSO Entity: Enter the value.
- Custom-SSO Property: Enter the value.
In PROPERTY VALUES section: - Custom-SSO Property Value: The user group details in the OIDC token claims received by OpsRamp contains the field information. Ensure that you provide the value of the field in this box.
- Example groups claim:
{ "groups": [ "OpsRamp-Admins", "OpsRamp-Viewers" ] }In this case, you enter OpsRamp-Admins as value. If there is a match, OpsRamp provisions the user group accordingly.
- OpsRamp Property Value: Select the appropriate role corresponding to the Custom-SSO Property Value.
- Click Save. The mapping is saved and displayed.
To add more property values click +Property Value. - Click Add Map Attributes.
- Click the three dots (menu icon) available at the end of each row to edit or delete a map attribute.
If the Role is not configured in Map Attributes section, the Default Role provided in the USER PROVISION section is considered for SSO.
Click Finish. The Custom SSO integration is installed and displayed under Installed Integrations.
Actions on Integration
You can perform actions like View Logs, Export, Edit, and Uninstall on the integration.
- See Actions on Integration for more information.
Audit Logs
View Inbound logs from the View Logs option for the integration. You can view if the event was successful or not.
See Audit Logs for more information.
Verification of SSO Integration
After completing the configuration, verify the OIDC integration:
- From your identity provider console, go to the OpsRamp OIDC application.
- Verify the following settings are correctly configured:
- Client ID: Unique identifier for the OpsRamp application.
- Client Secret: Confidential key for the OpsRamp application.
- Sign-in redirect URI: The OpsRamp callback URL.
- Sign-out redirect URI: The OpsRamp logout redirect URL.
- Confirm that the authorization server endpoints entered in OpsRamp match those in your identity provider:
- Issuer URL
- Authorization Endpoint
- Token Endpoint
- JWKS URI
- Logout URL
Provision a User
After configuring the OpsRamp Custom SSO OIDC integration, you can provision users using JIT provisioning.
In the OpsRamp UI …
- Navigate to Setup > Account.
- On the Clients page, search for the client and click on the client name.
- Copy the subdomain part of the Website URL. This subdomain is the value you configured in the identity provider’s redirect URI.
On your identity provider console …
Assign users to the OIDC application:
- Navigate to the application management section and select your OpsRamp OIDC application.
- Open the Assignments or Users tab.
- Assign the appropriate users or groups to the application.
Add a new user (if needed):
- In your identity provider, navigate to the user directory and add a new user.
- Enter the required personal information. The Username must be an email address.
- Assign the new user to the OpsRamp OIDC application.
In the OpsRamp UI …
- Navigate to Setup > Account.
- Click Users and Permissions tile and from Users card, after a short delay, verify that the provisioned user is added to the user list upon first login via JIT provisioning.
Unprovision a User
On your identity provider console …
- Navigate to the application management section and select your OpsRamp OIDC application.
- Open the Assignments or Users tab.
- Remove the user from the application assignment.
In the OpsRamp UI …
Refresh the Setup > Account > Users page to confirm the user is deactivated or removed from the list.
Notes:
- OIDC uses JIT provisioning; users are created automatically in OpsRamp upon their first successful login.
- Ensure the groups claim is included in the ID token by configuring the appropriate claims or scopes in your identity provider.
- Usernames created must be unique across clients.
- The Client Secret must be kept confidential. Rotate it immediately if it is exposed.